Enforce Advanced Security Across Your Apple Fleet
Harden your Apple devices to any standard with security configurations and automations designed to stay out of the user's way.
Get StartedWhy Kandji should secure your Mac systems
Endpoint devices likely make up over half of your attack surface. Kandji is the fastest and most efficient way to fortify your Apple endpoints against breaches.
An uninterrupted workflow
Users begin receiving notifications 5 days before your enforcement deadline to update or upgrade their Mac and its applications—so those updates won't interrupt important work. Plus, Kandji's beautiful interface makes user interaction streamlined and intuitive.
Click-and-go compliance
Deploy advanced security across your Mac fleet within minutes and customize it to your organization's needs. Start from pre-built templates with settings that map to NIST, CIS, and STIG frameworks—the foundations for any compliance program.
Autonomous enforcement
The Kandji Agent lives locally on a Mac and keeps it in its desired state. The agent holds record of all configurations you've set for it, remediating unapproved changes automatically. If users uninstall crucial apps or change security settings, the Kandji Agent fixes it.
A universe of additional security automations
Kandji expands on Apple MDM's capabilities, giving you more control over your fleet with dozens of added security automations. We took care of the scripting. All you need to do is point and click.
Security settings that just click

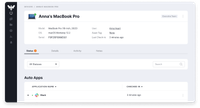
Kandji has hundreds of security settings and automations organized into Blueprint templates and tagged based on NIST, CIS, and STIG standards. Start from a predefined template or add your own security settings to a blank one. Customize Blueprints for different users based on their clearance.
Deploy software from the Auto App library and let Kandji automate the patching—forever. Use the same automated approach to enforce macOS updates across your environment.
Get unprecedented visibility into the current state of your fleet’s security. Keep tabs on all activity with detailed records, key updates, and an extensive log of remediations performed on each device.

Manage and secure your Apple devices at scale.
Fleet security is just one facet
Kandji keeps your device fleet in its desired state with powerful automation, extensive app library, and a UX that's as friendly for admins as it is for users.
[form]