2024: Kandji's Year in Review
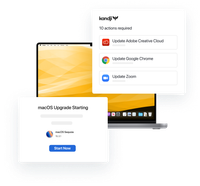
In 2024, Kandji continued to revolutionize Apple device management with groundbreaking innovations, powerful new integrations, and significant improvements to our core platform.
Keep reading
Table of Contents
A Media Access Control (MAC) address is a fundamental networking technology developed within the IEEE 802 specification in 1979. Without it, the data you send, or request would not reach its destination.
It consists of a unique string of 12 characters hardwired into the network interface card (NIC) on your device, which in turn supports Wi-Fi, Bluetooth, and wired networking. Those numbers are used to identify devices on the network, ensuring that data sent or requested goes to the right place.
The 12 digits also codify other valuable information, such as the type of device and NIC manufacturer. If visible, these unique addresses provide a lot of information about the device. Applications can—and sometimes do—use this data for user profiling, to track user movements and behaviour on the network. Network operators and other network observers may use it to monitor a device’s network activity and location.
Apple introduced MAC address randomization in iOS 8, to help secure user privacy. It is now available across Apple’s the latest versions of macOS, iOS, iPadOS, and watchOS. It masks the identity of the device by creating a different randomized address for each Wi-Fi network (SSID) that a device joins. That address is used only when accessing that particular network, which means it cannot be used to track activity across others.
Rather than using your hardware-coded MAC address, your system is recognized through use of the randomized one. As a result, users cannot be tracked from one Wi-Fi network to another. MAC Address Randomization is also used to mask device identity when using location-based services, such as Maps, when making peer-to-peer Wi-Fi connections such as with AirDrop or AirPlay, or when using Personal Hotspot or Internet Sharing.
The protection is not total. Apple says: “Wi-Fi scans that happen while trying to connect to a preferred Wi-Fi network aren’t randomised.”
Administrators frequently exploit the fact that every device on the same network has its own MAC address to help diagnose network issues. This helps identify network bottlenecks by making it possible to identify which sender(s) or receiver(s) of data may be contributing to network problems.
Of course, enterprises must also protect against network intrusion. To do so, they may use address filtering in which the router is instructed to only take traffic from specific MAC addresses, which means only approved devices get access to the network.
Some enterprises—for example, high-traffic retailers—may also offer Wi-Fi as a customer benefit. Such businesses may want to monitor MAC addresses to help gather customer behaviour data. In both cases, they can configure the Wi-Fi router to insist on the hardware address, rather than respecting the randomized one. This is also why administrators should ensure all employees are made aware that there are risks to using public Wi-Fi, as these networks may gather MAC addresses by denying to support for randomized addresses. In all these cases, IT may want to disable or deny support for the feature.
Some network administrators manage Wi-Fi routers that are configured to notify them when new devices join the network. Organizations that provide such managed Wi-Fi networks may need to update their security to work with these randomized MAC addresses.
Secure Wi-Fi administrators may, for example, find that if they run multiple networks (2.4GHz and 5GHz) on an SSID router they see multiple addresses for each device on the network—one for the 2.4GHz and another for the 5GHz. The implication is that admins seeking to apply time rules, blocks on devices, or other actions on their network may need to apply them multiple times.
Using an MDM solution such as Kandji, enterprises can require managed devices on their network to turn off private Wi-Fi when accessing the company network. Admins can also set networks to reject connections made using a private address, in which case the device will first try to join the network using the randomized address and then use its hardware MAC address. It is worth noting that each time it subsequently attempts to re-join the network the device will still attempt to use a random MAC address.
Users will not usually be aware their device is using randomization—which is on by default—because the process of connecting to the network remains the same.
It is possible to disable MAC Address Randomization. On an iPhone, for example, it means either (a) opening Settings > Wi-Fi, clicking the ‘I’ information icon, and toggling Private Wi-Fi Address to off or (b) asking the device to Forget This Network in Wi-Fi settings. If a device’s Network Settings are reset, or the device erased and set up as new, users will need to join the network again. The one exception to this is that, when a device connects to a Wi-Fi network during Setup Assistant, it will use its hardware MAC address. You can also enable or disable the feature using an MDM solution.
MAC Address Randomization can be implemented remotely using network profiles assigned by MDM. An IT admin may want to disable MAC Address Randomization on the company’s own internal Wi-Fi network to help manage that network. (In Kandji, for example, this is achieved by adding an instruction to Disable Mac Address Randomization in the Wi-Fi Library Item’s General setting.) This will be applied to the SSID (router) which will then insist on the genuine MAC address to honor connection requests.

In 2024, Kandji continued to revolutionize Apple device management with groundbreaking innovations, powerful new integrations, and significant improvements to our core platform.
Keep reading
Discover the trends shaping enterprise technology as Apple devices continue to gain ground in the corporate world.
Learn more
Watch the virtual event recap from our latest product announcement. Kandji unveils new assignment features and automations that make administration easy and efficient regardless of scale and complexity.
Watch the event