2024: Kandji's Year in Review
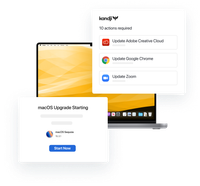
In 2024, Kandji continued to revolutionize Apple device management with groundbreaking innovations, powerful new integrations, and significant improvements to our core platform.
Keep reading
Table of Contents
The world of IT administration is rife with acronyms. But what those acronyms mean and how they differ is not always completely clear.
That’s especially true when an acronym or the full term it shortens doesn’t have a formal definition. Sometimes they’re defined by a standards organization like the Internet Engineering Task Force (IETF) or an industry group like the Wi-Fi Alliance. Other times an acronym is created by a company to help explain a new feature or product to the market.
This ambiguity is especially prevalent in the device-management business. Depending on the vendor or platform, you might see references to MDM, EMM, UEM, and others. Here’s a quick primer on what we think they currently mean.
The most common term: MDM, short for “mobile device management,” which refers to software tools that IT admins can use to provision, secure, and monitor an organization’s fleet of mobile devices in real time. The primary goal of MDM is to ensure security and compliance for all endpoints in an organization, including personal devices purchased by employees who use them for work email and to access enterprise applications.
“EMM” stands for “enterprise mobility management.” EMM tools can help integrate MDM with other enterprise systems, while adding tools to manage both mobile applications and content. EMM extends MDM’s centralized control to the software that runs on mobile devices. It might enforce regular software updates as well as restrictions on which apps can run—and which content can be viewed by device users.
Recently the tech industry has also been touting UEM (unified endpoint management), which goes further than MDM and EMM to encompass every endpoint computing device in an organization, including devices like smartphones and tablets, and computers like laptops and desktops. However, neither “UEM” nor “EMM” have caught on in common parlance. Most people use “MDM” as shorthand to refer to all device management capabilities.
Historically, IT admins used on-premises systems like Active Directory and a big firewall to manage and secure computers that always remained at the office. That meant that the computers had a guaranteed fast connection (wired or wireless) to the organization’s management systems, and were always protected by the firewall (at least protected from outside threats, even though it turns out that inside threats can be as dangerous).
As users began to use computers outside the confines of the office, many IT departments began configuring those computers to use Virtual Private Network (VPN) connections to the organization’s network, to facilitate management and security. But mobile devices like phones and tablets don’t necessarily work with such on-premises management solutions.
That’s how MDM began. It enables admins to address the potential vulnerabilities introduced by mobile devices and computers, most of which are used for both personal and professional purposes. (The so-called bring your own device, or BYOD, phenomenon.) It supports technologies such as containerization to protect corporate data, as well as the privacy of personal data.
At first MDM measures were simple, such as mandating password protection and enabling admins to lock or wipe devices remotely. But over the years MDM capabilities evolved to include implementing data encryption, configuring devices remotely, tracking device location, security monitoring, and more.
MDM solutions consist of a server component, which provides a central point of control for IT admins, and agents that are installed on mobile devices. In most cases, MDM server software runs in the cloud and issues commands to devices to adjust configurations, monitor activity, regulate access to enterprise apps and data, and enforce device security. Essentially, MDM enables organizations to enforce their compliance and data security policies as well as configure devices efficiently, without touching them (often referred to as over-the-air, or OTA).
Although some MDM solutions work across Apple, Microsoft, and Android platforms, platform-specific solutions provide more granular device control over devies that use the macOS, iOS, and iPadOS operating systems (including desktops). For example, an Apple MDM solution works hand-in-glove with Apple Business Manager, the web portal that enables admins to maintain an inventory of an organization’s Apple devices, to enroll those devices into management, and to generate Managed Apple IDs for end users.
Regardless of platform, the more admins can accomplish centrally, with MDM automation features, the less time they to spend managing devices manually.
EMM derived from a recognition that MDM needed to be a part of an enterprise’s overall security and compliance posture, including data security. Although the line between MDM and EMM is blurry, it’s generally accepted that EMM added synchronization with directory services such as Microsoft Active Directory or Google Workspace. With that advancement, device management stopped being a separate endeavor and became an extension of security and compliance all the way to the outer edge of the network.
While the specific capabilities of different EMM solutions vary, they do provide some common functionality:
IAM provides a framework for implementing user authentication as well as policy-based rights and permissions. An EMM with IAM features lets IT teams assign individual users to groups, with each group accorded the same set of permissions and restrictions—for accessing networks, configuring devices, and so on.
MAM enables distributing, securing, and updating software that runs on mobile devices, whether commercial software or bespoke applications. With MAM software, admins have the power to provision a fleet of devices with the same apps or updates in one swoop, no hands-on installation required. MAM solutions may also include the ability to prevent the installation of unsafe apps and even block or allow individual app features.
Consumers use mobile devices to enjoy all manner of content and services. Organizations, however, often distribute sensitive data or documents to employees. Whether or not a user (or an application) can access certain content should depend on the rights and permissions associated with user roles. Additionally, MAM software may use the user’s location to determine which content should be sent.
Keep in mind that MDM solutions may implement some or all components of EMM that this article just defined (IAM, MAM, and MCM).
MDM and EMM play a key role in reducing an organization’s vulnerability to data loss and other security breaches, as well as enhancing its ability to deliver the appropriate resources to devices . Even the most carefully crafted policies have limited utility if they can’t be implemented at scale, and doing so routinely across a fleet of devices, with minimum effort and maximal automation, is the operational goal of MDM and EMM.
Well-crafted MDM and EMM solutions free up time for admins, so they can engage in more strategic efforts. These solutions also reduce the possibility of human error, thanks to such automated capabilities such as scheduled updates and preplanned configuration changes, as well as the ability to import user and device profiles rather than entering them manually.

In 2024, Kandji continued to revolutionize Apple device management with groundbreaking innovations, powerful new integrations, and significant improvements to our core platform.
Keep reading
Discover the trends shaping enterprise technology as Apple devices continue to gain ground in the corporate world.
Learn more
Watch the virtual event recap from our latest product announcement. Kandji unveils new assignment features and automations that make administration easy and efficient regardless of scale and complexity.
Watch the event