2024: Kandji's Year in Review
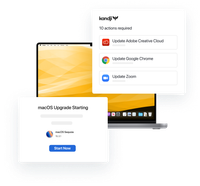
In 2024, Kandji continued to revolutionize Apple device management with groundbreaking innovations, powerful new integrations, and significant improvements to our core platform.
Keep reading
Table of Contents
These days, many employees are empowered to work from anywhere, across multiple platforms, locations, time zones. To make that work, they’re increasingly rely on cloud-based SaaS systems. But like any other organization resource, such systems must be secured against unauthorized access. Federated authentication lets users access such systems using a single identity; instead of requiring individual logins for every service, users require just one.
Federated authentication is a system in which user identity and authorization is managed by an identity provider (IdP), which acts as a trusted third party.
It works like this: When a user visits a service they want to use, they’re automatically forwarded to the IdP for authentication. The IdP verifies the user and returns a secure authorization token (usually an XML file) to the service, which then provides the user access.
Without federated authentication, the user would need to authenticate each time they sought access to a different service provider. With it, users can access multiple services once they are authorized with their IdP. This obviates the need to remember multiple logins and passwords.
Federated authentication minimizes the need to remember or manage passwords. It also allows users to move more freely between systems, without the need for constantly resubmitting credentials. And it does so while also preserving an organization’s control over access to enterprise resources via authentication, authorization and trust.
While single sign-on (SSO) lets users authenticate across an organization’s systems using a single set of credentials, federated authentication makes it possible to use a single credential and IdP to access numerous services and applications from multiple entities. In other words, while SSO lets employees securely access a single set of systems, federated authentication lets them use any system that supports that IdP.
The primary protocols used in federated authentication include Security Assertion Markup Language ( SAML), Open ID, and OAuth 2. All three provide the technologies IdPs need to enable secure authorization across multiple services.
Security Assertion Markup Language (SAML): Self-contained and widely deployed, SAML is an open standard that enables IdPs to authenticate users. It relies on Extensible Markup Language (XML).
OAuth 2: OAuth is an open-standard authorization protocol designed to authenticate multiple services without sharing the initial credential. The idea is that authorization provided for one service is recognized elsewhere through use of authentication tokens.
OpenID: OpenID adds an identity-authentication layer to OAuth 2 to provide additional security. It is used by many prominent services, including Facebook, Microsoft, Google, and PayPal.
If your organization uses Microsoft Azure Active Directory (Azure AD) or Google Workspace as its IdP, you can then use federated authentication to connect with Apple Business Manager, as explained in detail here. Once enrolled, employees use their Azure or Workspace credentials as Managed Apple IDs, which can themselves be used to access Apple services. This means employees only need their Azure or Google credentials to login. The integration uses SAML to pass credentials between the IdP and Apple Business Manager.
The big benefit of federated authentication is that it can help reduce a company’s attack surface while providing users and IT with improved user experiences.
Service providers can pass the technology management overhead of building and maintaining their own authorization systems to trusted third parties with sufficient resources for the task. This eliminates redundant systems, lowers IT support overhead, and adds the ability to remotely set policies and controls on managed devices.
The US government understands the need to secure the digital enterprise. Since 2004 it has required use of secure credentials to access government systems and various government security departments are collaborating on a federated identification standards.
Federated authentication delivers security and convenience within a near-frictionless user experience. Through the provision of one key point of trust for authorization, it helps secure services and business systems providers who benefit from trusted multi-factor protection and a reduction in fraud detection and tech support costs.

In 2024, Kandji continued to revolutionize Apple device management with groundbreaking innovations, powerful new integrations, and significant improvements to our core platform.
Keep reading
Discover the trends shaping enterprise technology as Apple devices continue to gain ground in the corporate world.
Learn more
Watch the virtual event recap from our latest product announcement. Kandji unveils new assignment features and automations that make administration easy and efficient regardless of scale and complexity.
Watch the event